Mobile Phone Hacking: How Titan’s Experts Uncover The Hidden Threats!
A professional guide to mobile phone security analysis, spyware detection and the evidence you need to protect yourself, your business and your privacy
Mobile phone hacking is no longer a niche concern. It is something that affects business owners, professionals and private individuals alike, and the difficulty is that suspicion often starts with a feeling rather than clear proof.
Perhaps someone seems to know information they should not know. Perhaps your phone is behaving oddly. Or perhaps you simply have that nagging sense that your mobile device has been compromised or monitored.
When that happens, the important question is not just ‘is my phone hacked?’ It is also ‘how do I actually check properly?’
There is a world of difference between guesswork and a professional mobile phone security analysis. If you are serious about finding hidden threats, you need a process that can identify spyware, malware, risky permissions and suspicious behaviour in a way that stands up to scrutiny.
At Titan Private Investigation Ltd, we work with individuals, legal professionals and businesses across the United Kingdom who find themselves in exactly this position. The concerns vary — a spouse who seems to know too much, a business rival who appears to be one step ahead, an employee who suspects workplace surveillance, or a professional who simply cannot shake the feeling that their private communications are no longer private. In every case, the answer is the same: you need evidence, not assumption.
When a Mobile Phone Compromise Is Suspected
People usually come to this issue from one of two directions.
The first is a technical concern. The device itself is behaving strangely — the battery drains faster than it should, the phone runs warm even when idle, data usage has spiked without explanation, or unfamiliar applications have appeared. These are not always signs of hacking, but they are signs that something warrants a closer look.
The second is an informational concern. Someone appears to know things they should not know. Private conversations have been referenced. Confidential business decisions seem to have leaked. Movements or plans that were never shared have somehow become known to another party. In these cases, the phone becomes a likely source of the leak, even if there are no obvious technical warning signs.
Either way, the concern is the same: is my mobile phone being monitored, and can it be proven?
It is worth noting that the emotional toll of this kind of uncertainty should not be underestimated. Living with the suspicion that your private communications are being read, your location tracked or your conversations listened to is deeply unsettling. It affects decision-making, relationships and professional confidence. Getting a definitive answer — whatever that answer turns out to be — is almost always better than continuing to operate under a cloud of doubt.
What Professional Phone Analysis Actually Looks For
A proper examination goes much deeper than checking a couple of settings or deleting a suspicious app. Professional mobile phone analysis is designed to inspect the device in a structured and comprehensive way.
Using specialist technology such as the ME M3 Pro, both Android and Apple iOS devices can be assessed for a range of threats, including:
- Malware
- Spyware
- Government-grade spyware
- Suspicious behaviour
- Dangerous or risky applications
- App permissions that may expose the user
The system uses artificial intelligence to support that analysis, helping identify not just known threats but behaviours and configurations that may point to compromise. This is an important distinction. Spyware developers are constantly updating their tools to evade detection. A purely signature-based approach — one that only looks for known threats — will always lag behind. AI-assisted behavioural analysis adds a further layer of scrutiny that can flag anomalies even when the specific threat has not yet been formally catalogued.
The Permissions That Matter Most
One of the most important parts of any mobile device inspection is understanding what apps are actually allowed to do.
A phone can become vulnerable not only because of overt spyware, but also because an app has been granted access it should never have had in the first place. Many people install applications without reading the permissions they are agreeing to, and over time those permissions accumulate. An app that seemed harmless when downloaded may have been quietly collecting data ever since.
That is why a proper analysis reviews active permissions, including access to:
- Microphone
- Camera
- Location data
- Accessibility functions
- Administrative controls
These are not minor details. If the wrong application has access to your microphone, camera or location, that can create a serious privacy and security issue even before a more advanced form of spyware is discovered. In some cases, the most significant finding in a report is not a piece of sophisticated spyware at all — it is a seemingly ordinary app that has been granted far more access than it needs and is quietly transmitting data to third parties.
Understanding the permissions landscape of a device gives both the investigator and the client a clearer picture of where the vulnerabilities lie and what remedial steps may be appropriate.
Hidden Threats Can Include Government-Level Spyware
For many people, the phrase ‘government spyware’ sounds dramatic, but it is very much part of the modern mobile security landscape. High-profile cases involving tools such as Pegasus have demonstrated that sophisticated surveillance software is not confined to intelligence agencies targeting foreign adversaries. Journalists, lawyers, business executives, activists and private individuals have all been identified as targets.
The analysis process checks for a list of known government spyware families, including:
- Pegasus
- Predator
- FinSpy
- Candiru
- Stealth Falcon
- Circles
- Varint
- Quadream
- Hermit
- Exodus
In total, the system checks against 15 known government spyware threats.
That does not mean every concerned phone owner is dealing with something at that level, of course. The vast majority of cases involve more commonplace forms of monitoring. But if you are carrying out a serious security analysis, it makes sense to rule out the full range of possibilities rather than just the obvious ones. A thorough investigation leaves no stone unturned.
It Also Checks for Commercial Spyware and Dangerous Apps
Not all phone monitoring comes from elite spyware. In many cases, the concern is far more domestic, personal or workplace-related. Commercial spyware — sometimes marketed as ‘parental control’ or ’employee monitoring’ software — is widely available, relatively inexpensive and straightforward to install on a target device. In the wrong hands, it becomes a tool for stalking, coercive control, corporate espionage or harassment.
The same analysis can also identify known spyware, malware and dangerous apps, including:
- FlexiSpy
- mSpy
- Spyera
- Guster
The system checks against 25 known dangerous applications in this category.
That is particularly relevant in cases involving suspected partner surveillance, employee concerns, internal data leakage or general privacy breaches. The threat is often not theoretical. It may be a commercially available app installed for the purpose of monitoring calls, messages, movements or activity — and it may have been placed on the device by someone with physical access to it, such as a partner, family member, employer or colleague.
In domestic abuse and coercive control cases, this type of monitoring is increasingly common. Identifying it quickly and documenting it properly can be a critical step in securing legal protection.
How Mobile Phone Analysis Used to Work
Traditionally, this sort of forensic phone analysis required the physical device to be sent away to a lab.
That process was effective, but inconvenient. A typical workflow involved:
- Sending the phone by Special Delivery
- Providing the access code
- Having the lab receive the device the following day
- Completing the analysis
- Returning the device by post
In practical terms, that often meant being without the phone for around 48 hours.
For some people, that was manageable. For others, it simply was not. If you rely on your phone for business, security, family contact or day-to-day operations, being separated from it for two days is far from ideal. Not everyone has a spare device ready to take a SIM card. And in situations where urgency matters — where evidence may be at risk of being deleted, or where a legal deadline is approaching — a two-day turnaround can feel like an eternity.
The Advantage of Remote Mobile Device Analysis
One of the major improvements now available is remote phone analysis.
Rather than posting the handset away, a technician can contact the phone owner directly, take the necessary information, and carry out the relevant analysis remotely. This approach represents a significant step forward in terms of accessibility and convenience, particularly for clients who are dealing with time-sensitive situations or who simply cannot afford to be without their device.
This approach offers some clear benefits:
- No need to send the phone away
- No 48-hour gap without your device
- Faster turnaround
- Less disruption to normal life or business
- Greater privacy — the device never leaves your possession
With the ME M3 Pro remote process, the aim is to have the matter dealt with and the report issued within 24 hours of instruction. That is a significant improvement for anyone facing an urgent security concern.
It is also worth noting that remote analysis removes one potential complication: the chain of custody question. When a device is posted, there is always a period during which it is out of the owner’s direct control. Remote analysis keeps the device in the client’s hands throughout, which can be relevant if the findings are later used in legal proceedings.
What Remote Analysis Can and Cannot Do
It is important to be clear about the limits as well as the benefits.
A remote download and inspection can detect spyware, malware, dangerous apps and suspicious configurations. It can also produce a detailed professional report. However, the remote process does not remove spyware or malware from the device.
When devices were physically handled, removal options were broader. Remote analysis is primarily about detection, documentation and evidence.
That still makes it extremely valuable, because before you can take action, you need to know what is on the device and be able to prove it properly. Once a report has been produced, the client is in a far stronger position — whether that means approaching law enforcement, taking legal advice, confronting an employer, or simply making an informed decision about how to proceed.
In some cases, the most appropriate next step after a remote analysis is to have the device physically examined and cleaned. The remote report provides the foundation for that decision, giving both the client and any subsequent technician a clear picture of what they are dealing with.
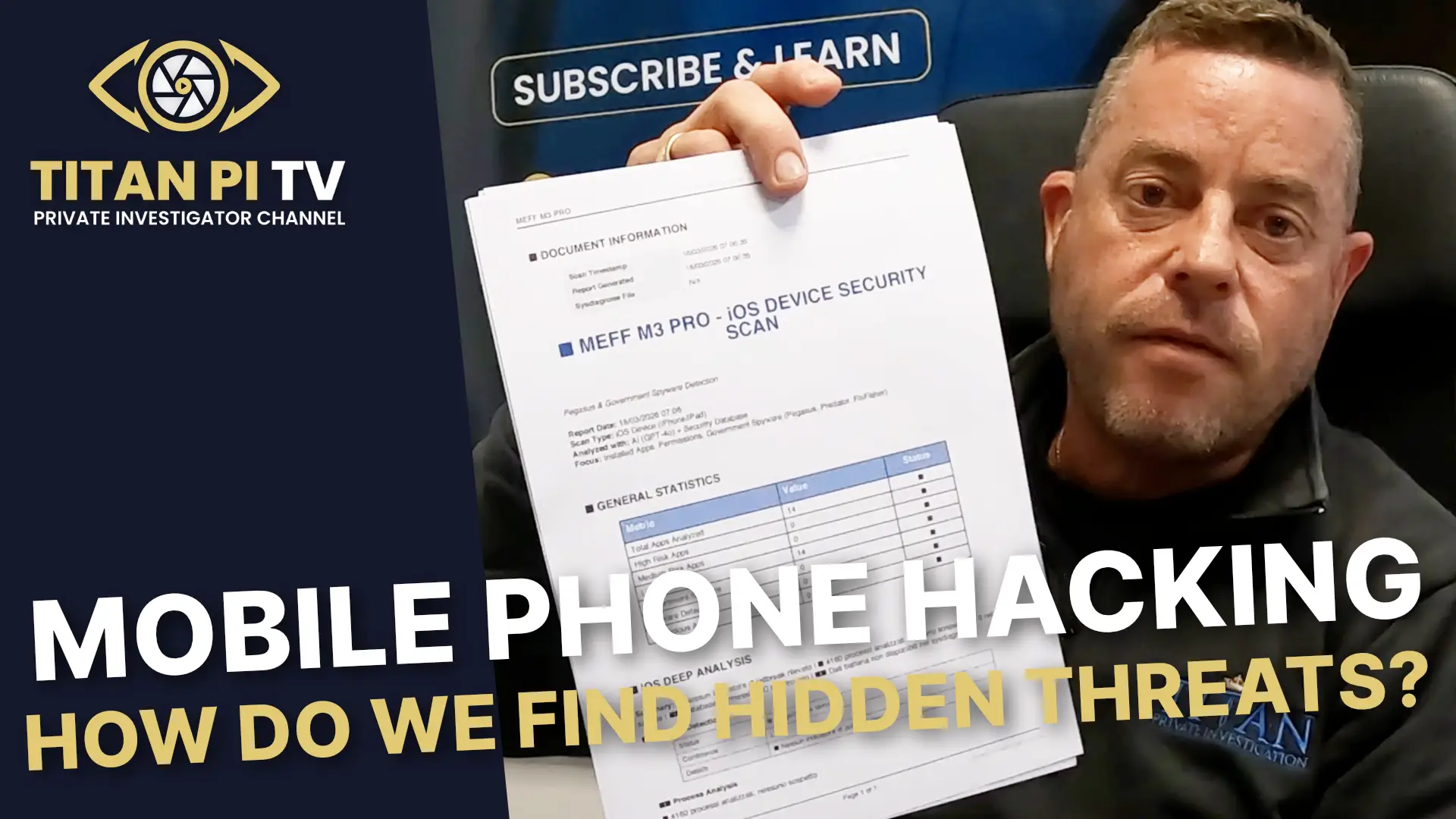
What You Receive in the Report
A professional mobile phone hacking report is not a vague checklist or a casual opinion. It is a structured document designed to show exactly what has been analysed and what has been found.
The report includes:
- General statistics showing how many apps were analysed
- Risk categorisation dividing findings into high, medium and low risk
- Government spyware detection results
- Malware detection results
- Suspicious app findings
- iOS deep analysis where applicable
- AI-driven in-depth analysis
- App-by-app explanation of flagged items and why they were rated as they were
- A complete checklist of government spyware and dangerous apps reviewed
- A scan integrity certificate
- System logs
- A report checksum
- Security recommendations to help keep the device safer going forward
One example involved a report identifying 14 low-risk apps. The report did not simply list them — it explained what each app was and why it had been categorised as low risk. That is what makes a report genuinely useful. It provides context rather than simply generating alarm, and it allows the client to understand the findings rather than simply being handed a verdict.
This level of detail is also important when the report needs to be shared with a third party — whether that is a solicitor, a court, an employer or a law enforcement agency. A well-structured, clearly explained report carries far more weight than a summary opinion.
Why This Matters if Law Enforcement Becomes Involved
If a phone has genuinely been hacked or monitored, there may come a point when the findings need to go beyond private reassurance.
A professionally prepared report can be provided to law enforcement agencies such as the police. It is also fully admissible in a criminal court.
That matters because suspicion alone does not get very far. If there has been unlawful monitoring, harassment, stalking, data theft or unauthorised access, the quality of the evidence can make all the difference. The Computer Misuse Act 1990 makes it a criminal offence to access a computer — including a mobile phone — without authorisation. The Investigatory Powers Act 2016 and the Regulation of Investigatory Powers Act 2000 also contain provisions relevant to unlawful interception. A properly documented report gives investigators and prosecutors something concrete to work with.
In civil proceedings — for example, in cases involving divorce, business disputes or employment tribunals — the same report can serve as evidence of a privacy breach or data theft. The admissibility and credibility of that evidence will depend in large part on how it was gathered and documented. That is why professional analysis matters far more than a DIY approach.
The Legal Point That Should Not Be Ignored
There is one point that needs stating plainly. A mobile phone analysis of this kind can only be carried out where the person requesting it owns the phone or has the legal authority to authorise the work.
You cannot lawfully instruct this sort of examination on someone else’s device just because you are curious or suspicious. Doing so can create serious legal problems and potentially amount to multiple offences under the Computer Misuse Act and related legislation.
That boundary is crucial. Investigating a possible compromise of your own device is one thing. Crossing into unauthorised access of another person’s device is quite another — and it is a line that Titan Private Investigation Ltd will not cross. All work is carried out strictly within the bounds of the law, and clients are advised accordingly from the outset.
How Much Does This Type of Phone Hacking Analysis Cost?
The cost for this remote mobile phone analysis service is £600 plus VAT, which comes to £720.
If multiple devices need to be analysed, there may be scope to reduce the fee depending on the circumstances.
For anyone dealing with a serious privacy or security concern, the more useful way to think about cost is this: what is the price of not knowing? If confidential conversations, business information, location data or personal messages are being exposed, getting clarity quickly can be invaluable. The cost of a professional analysis is modest compared to the potential consequences of a serious privacy breach — whether those consequences are financial, reputational, legal or personal.
It is also worth considering the cost of acting on the wrong assumption. Without a proper analysis, some people take drastic steps — ending relationships, leaving jobs, making accusations — based on suspicion alone. A professional report either confirms the concern or rules it out, allowing the client to make decisions based on facts rather than fear.
When to Seek Help
If you think your phone has been compromised in any way, or you suspect it is being monitored, the best time to act is when the concern becomes credible — not months later.
Warning signs may include:
- Someone knowing private information they should not have
- Unusual battery drain, data usage or device behaviour
- Concerns about spyware installed by another individual
- A need for evidence suitable for police or court use
- The need to assess more than one mobile device quickly
- A desire to have a professional opinion rather than relying on guesswork
Even where the result shows low-risk findings rather than serious compromise, that still has value. It helps narrow the issue, rule out possibilities and give you a clearer path forward. In some cases, the peace of mind that comes from a clean report is itself worth the investment.
Equally, if the report does identify a genuine threat, you will be in a far stronger position having acted promptly. Evidence can be lost. Spyware can be removed by the person who installed it. The sooner a professional analysis is carried out, the better the chances of capturing the full picture.
Mobile Phone Hacking: Final Thoughts
Mobile phone hacking can feel invisible, and that is exactly what makes it unsettling. The modern smartphone holds conversations, photographs, movements, business information, passwords and patterns of daily life. If it is compromised, the consequences can be personal, professional and legal all at once.
The good news is that hidden threats do not have to remain hidden. With the right tools, a structured analysis and a proper report, it is possible to move from suspicion to evidence.
And when you are dealing with something as important as privacy and security, evidence is what counts.
Titan Private Investigation Ltd provides professional, discreet and legally compliant mobile phone security analysis for individuals, businesses and legal professionals across the United Kingdom. If you have concerns about the security of your device, we are here to help you find the answers you need.
About Titan Private Investigation Ltd
Titan Private Investigation Ltd is a leading provider of corporate and private investigation services in the UK. Based in Derby, the company serves clients nationwide, offering a full range of investigative solutions including surveillance, fraud investigation, digital forensics, and more. We are a private investigation agency with a reputation for professionalism, discretion, and delivering results. Titan is the trusted partner of choice for businesses seeking to protect their interests and ensure compliance.
London Mobile Device Hacking – Call the Titan Investigations London Office 020 39046622
Birmingham Mobile Device Hacking – Call the Titan Investigations Birmingham Office 0121 7162442
Cambridge Mobile Device Hacking – Call the Titan Investigations Cambridge Office 01223 662022
Derby Mobile Device Hacking – Call the Titan Investigations Derby (Head Office) 01332 504256
Leeds Mobile Device Hacking – Call the Titan Investigations Leeds Office 0113 4574066
Leicester Mobile Device Hacking – Call the Titan Investigations Leicester Office 0116 2436520
Nottingham Mobile Device Hacking – Call the Titan Investigations Nottingham Office 0115 9646950
Manchester Mobile Device Hacking – Call the Titan Investigations Manchester Office 0161 3023008
Sheffield Mobile Device Hacking – Call the Titan Investigations Sheffield Office 0114 3499400
Truro Mobile Device Hacking – Call the Titan Investigations Truro Office 01872 888706
Alternatively, you can contact us directly using our fully confidential contact form at enquiries@titaninvestigations.co.uk or chat directly using our Live Chat facility, and one of our UK Private Investigators will get right back to you.